Running NextCloud behind Cloudflare
This is a very quick tip that I just hope gets picked up by Google and saves somebody else some time.
If (like me) you run NextCloud on your own infrastructure to provide filesharing and collaboaration services, and you run it behind Cloudflare, you may find yourself banging your head against the screen trying to work out why everything works except for uploading files through the web interface.
Instead, you’ll get an enigmatic an unknown error occurred message in
the web interface, and absolutely nothing in the NextCloud logs. Looking in
your browser network logs may give you a clue - the PUT request to the
/remote.php/webdav URL will be getting HTTP/403 (forbidden) responses.
I am here to save you some debugging…
It turns out that if you use Cloudflare’s WAF “Managed Rules” (which I think
are on by default, and which even if they’re not - you probably should be
using them anyway,) one of the rules in their ‘Managed OWASP’ ruleset is
triggered by the PUT request from the NextCloud Web UI, and Cloudflare
blocks it.
The Solution⌗
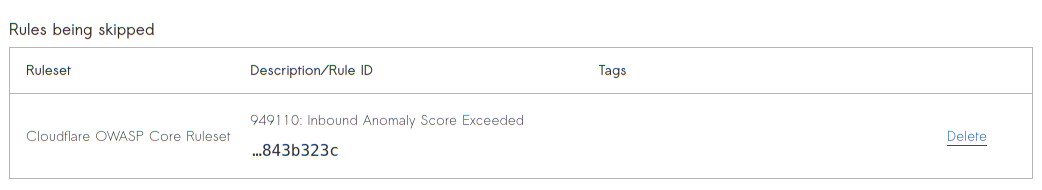
The solution is simple. Go to your WAF configuration in Cloudflare
(Security > WAF), and under Managed Rules you need to add an exception.
Click “Add an exception”, and set some suitable criteria to match requests
(e.g. the specific host or URI path of your NextCloud installation,) and
then “Skip specific rules from a managed ruleset”. The rule you want to skip
is 949110: Inbound Anomaly Score Exceeded in the Cloudflare OWASP Core Ruleset:
Deploy your new rule, and hey-presto: working NextCloud through Cloudflare.